- Retrait gratuit dans votre magasin Club
- 7.000.000 titres dans notre catalogue
- Payer en toute sécurité
- Toujours un magasin près de chez vous
- Retrait gratuit dans votre magasin Club
- 7.000.0000 titres dans notre catalogue
- Payer en toute sécurité
- Toujours un magasin près de chez vous
53,45 €
+ 106 points
Description
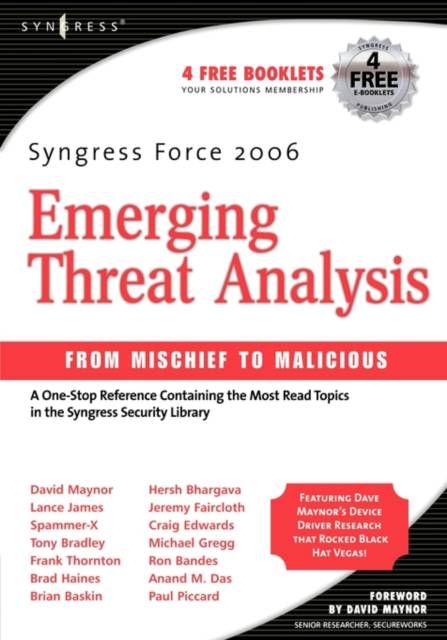
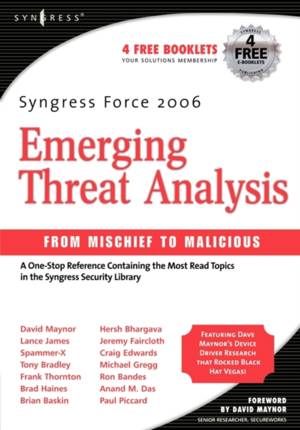
A One-Stop Reference Containing the Most Read Topics in the Syngress Security Library This Syngress Anthology Helps You Protect Your Enterprise from Tomorrow's Threats Today This is the perfect reference for any IT professional responsible for protecting their enterprise from the next generation of IT security threats. This anthology represents the "best of" this year's top Syngress Security books on the Human, Malware, VoIP, Device Driver, RFID, Phishing, and Spam threats likely to be unleashed in the near future.. * From Practical VoIP Security, Thomas Porter, Ph.D. and Director of IT Security for the FIFA 2006 World Cup, writes on threats to VoIP communications systems and makes recommendations on VoIP security.
* From Phishing Exposed, Lance James, Chief Technology Officer of Secure Science Corporation, presents the latest information on phishing and spam.
* From Combating Spyware in the Enterprise, Brian Baskin, instructor for the annual Department of Defense Cyber Crime Conference, writes on forensic detection and removal of spyware.
* Also from Combating Spyware in the Enterprise, About.com's security expert Tony Bradley covers the transformation of spyware.
* From Inside the SPAM Cartel, Spammer-X shows how spam is created and why it works so well.
* From Securing IM and P2P Applications for the Enterprise, Paul Piccard, former manager of Internet Security Systems' Global Threat Operations Center, covers Skype security.
* Also from Securing IM and P2P Applications for the Enterprise, Craig Edwards, creator of the IRC security software IRC Defender, discusses global IRC security.
* From RFID Security, Brad "Renderman" Haines, one of the most visible members of the wardriving community, covers tag encoding and tag application attacks.
* Also from RFID Security, Frank Thornton, owner of Blackthorn Systems and an expert in wireless networks, discusses management of RFID security.
* From Hack the Stack, security expert Michael Gregg covers attacking the people layer.
* Bonus coverage includes exclusive material on device driver attacks by Dave Maynor, Senior Researcher at SecureWorks.
* From Phishing Exposed, Lance James, Chief Technology Officer of Secure Science Corporation, presents the latest information on phishing and spam.
* From Combating Spyware in the Enterprise, Brian Baskin, instructor for the annual Department of Defense Cyber Crime Conference, writes on forensic detection and removal of spyware.
* Also from Combating Spyware in the Enterprise, About.com's security expert Tony Bradley covers the transformation of spyware.
* From Inside the SPAM Cartel, Spammer-X shows how spam is created and why it works so well.
* From Securing IM and P2P Applications for the Enterprise, Paul Piccard, former manager of Internet Security Systems' Global Threat Operations Center, covers Skype security.
* Also from Securing IM and P2P Applications for the Enterprise, Craig Edwards, creator of the IRC security software IRC Defender, discusses global IRC security.
* From RFID Security, Brad "Renderman" Haines, one of the most visible members of the wardriving community, covers tag encoding and tag application attacks.
* Also from RFID Security, Frank Thornton, owner of Blackthorn Systems and an expert in wireless networks, discusses management of RFID security.
* From Hack the Stack, security expert Michael Gregg covers attacking the people layer.
* Bonus coverage includes exclusive material on device driver attacks by Dave Maynor, Senior Researcher at SecureWorks.
Spécifications
Parties prenantes
- Auteur(s) :
- Editeur:
Contenu
- Nombre de pages :
- 642
- Langue:
- Anglais
Caractéristiques
- EAN:
- 9781597490566
- Date de parution :
- 01-10-06
- Format:
- Livre broché
- Format numérique:
- Trade paperback (VS)
- Dimensions :
- 179 mm x 229 mm
- Poids :
- 861 g
Les avis
Nous publions uniquement les avis qui respectent les conditions requises. Consultez nos conditions pour les avis.